Manufacturer based on mac address
After September , the value The owners of an already assigned IAB may continue to use the assignment. A universally administered address is uniquely assigned to a device by its manufacturer.
MAC Address Lookup
The first three octets in transmission order identify the organization that issued the identifier and are known as the organizationally unique identifier OUI. A locally administered address is assigned to a device by a network administrator, overriding the burned-in address. Universally administered and locally administered addresses are distinguished by setting the second- least-significant bit of the first octet of the address.
If the bit is 0, the address is universally administered.
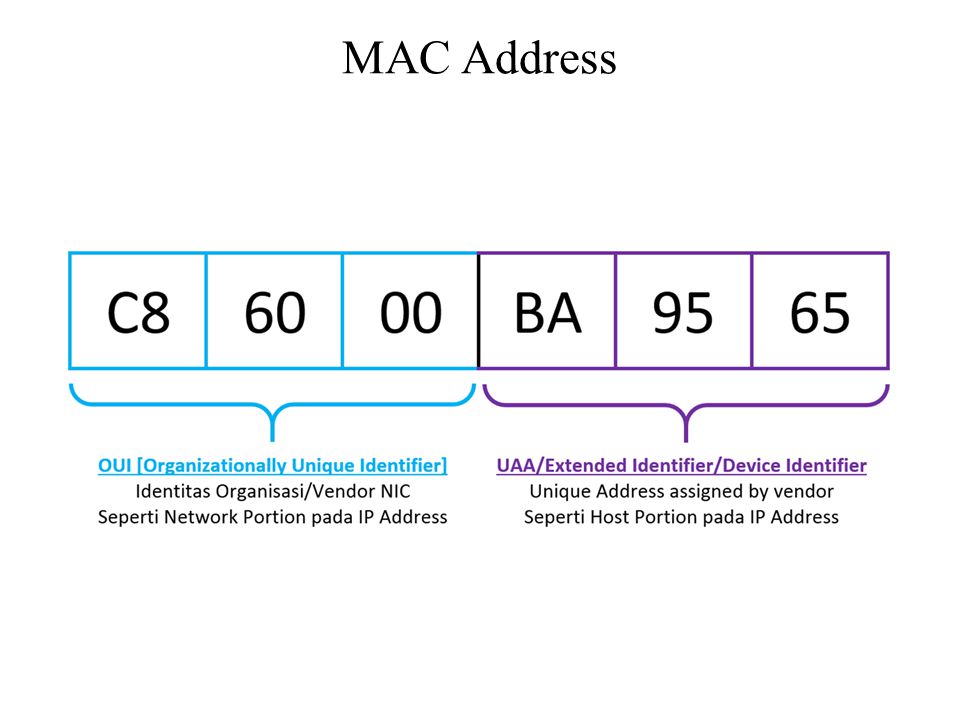
If it is 1, the address is locally administered. In the example address the first octet is 06 hex , the binary form of which is , where the second-least-significant bit is 1. Therefore, it is a locally administered address.
Wireshark · OUI Lookup Tool
This eliminates the need for an address resolution protocol since the MAC address for any DECnet host can be simply determined. When the least significant bit of an address's first octet is 0 zero , the frame is meant to reach only one receiving NIC. A unicast frame is transmitted to all nodes within the collision domain. In a modern wired setting the collision domain usually is the length of the Ethernet cable between two network cards. In a wireless setting, the collision domain is all receivers that can detect a given wireless signal.
If a switch does not know which port leads to a given MAC address, the switch will forward a unicast frame to all of its ports except the originating port , an action known as unicast flood. If the least significant bit of the first octet is set to 1, the frame will still be sent only once; however, NICs will choose to accept it based on criteria other than the matching of a MAC address: This is called multicast addressing.
The IEEE has built in several special address types to allow more than one network interface card to be addressed at one time:.
- table contents word mac 2008;
- Recent MAC addresses lookup!
- free mac games apple store.
- MAC Address / OUI Lookup!
- MAC address - Wikipedia.
- mcdonalds $1 big mac december 2013!
These are all examples of group addresses , as opposed to individual addresses ; the least significant bit of the first octet of a MAC address distinguishes individual addresses from group addresses. That bit is set to 0 in individual addresses and set to 1 in group addresses. Group addresses, like individual addresses, can be universally administered or locally administered. Common networked consumer devices such as PCs, smartphones and tablet computers use EUI addresses. On broadcast networks, such as Ethernet, the MAC address is expected to uniquely identify each node on that segment and allows frames to be marked for specific hosts.
It thus forms the basis of most of the link layer OSI Layer 2 networking upon which upper layer protocols rely to produce complex, functioning networks. Although intended to be a permanent and globally unique identification, it is possible to change the MAC address on most modern hardware. Changing MAC addresses is necessary in network virtualization.
It can also be used in the process of exploiting security vulnerabilities.
Nmap Network Scanning
This is called MAC spoofing. A MAC address is like a social security number which remains unchanged for a person's life time here, the device , while an IP address is like a postal code which can be changed. MAC address randomization during scanning was added in Android starting from version 6. The actual implementations of the MAC address randomization technique vary largely in different devices [16].
Moreover, various flaws and shortcomings in these implementations may allow an attacker to track a device even if its MAC address is changed, for instance its probe requests' other elements [17] [18] , or their timing [19] [16]. If random MAC addresses are not used, researchers have confirmed that it is possible to link a real identity to a particular wireless MAC address.
Many network interfaces including wireless ones support changing their MAC address. The configuration is specific to the operating system. On most Unix -like systems, the ifconfig command may be used to add and remove "link" Ethernet MAC family address aliases. For instance, the "active" ifconfig directive may then be used on NetBSD to specify which of the attached addresses to activate. Using wireless access points in SSID -hidden mode see network cloaking , a mobile wireless device may not only disclose its own MAC address when traveling, but even the MAC addresses associated to SSIDs the device has already connected to, if they are configured to send these as part of probe request packets.
Alternative modes to prevent this include configuring access points to be either in beacon-broadcasting mode, or probe-response with SSID mode. In these modes, probe requests may be unnecessary, or sent in broadcast mode without disclosing the identity of previously-known networks. The standard IEEE format for printing EUI addresses in human-friendly form is six groups of two hexadecimal digits, separated by hyphens - in transmission order e.
This form is also commonly used for EUI e. AB , and three groups of four hexadecimal digits separated by dots. The standard notation, also called canonical format, for MAC addresses is written in transmission order with the least significant bit of each byte transmitted first, and is used in the output of the ifconfig , iproute2 , and ipconfig commands, for example. However, since IEEE For example, an address in canonical form A-BC would be transmitted over the wire as bits in the standard transmission order least significant bit first.
But for Token Ring networks, it would be transmitted as bits in most-significant-bit first order. I would e-mail the writers of one of those pieces of software. One question - how reliably do Mac addresses, which can commonly be reset in hardware, reflect this database? It is indeed, fairly easy to change your mac-address. There is however no way of knowing it then. Nothing you can do about this. There may be industries where it's typical to change it, but in most cases it never happens.
May 1 '12 at 3: Sometimes a whole batch comes with 1 mac address. The Wireshark development team maintains a much more complete list: Gerald Combs Gerald Combs 5, 18 Matt Hamende Matt Hamende 1 Sign up or log in Sign up using Google. Sign up using Facebook. Sign up using Email and Password.
- Navigation menu.
- mac new viva glam collection;
- Your Answer.
- mac miller senior skip day album wiki.
Post as a guest Name. Email Required, but never shown. Post Your Answer Discard By clicking "Post Your Answer", you acknowledge that you have read our updated terms of service , privacy policy and cookie policy , and that your continued use of the website is subject to these policies. Related 5.